Authenticators are applications that serve several purposes for Android and iOS devices. They’re mainly used for two types of authentication, known as multi-factor authentication (MFA) and multi-step authentication (MSA). They provide advanced security for user sites.
What this means is that it’s not enough to know or have an account password. With increased hacking and cybercrime, authentication codes are necessary to guarantee the security of your online activities and personal data.
Having a protected account means no thief or hacker can access your data, whether on an Android or iOS device. Typically, you only need a password to sign in and log into your online account. With an Authentication app, you can use both the password and the OTP generating app simultaneously.
Here, you’ll need to apply 2- factor authentication (2FA), which includes the knowledge factor where you as the user know your password. The other factor is the possession factor where you have the smartphone.
Let’s take a closer look at how the Google Authenticator app works.
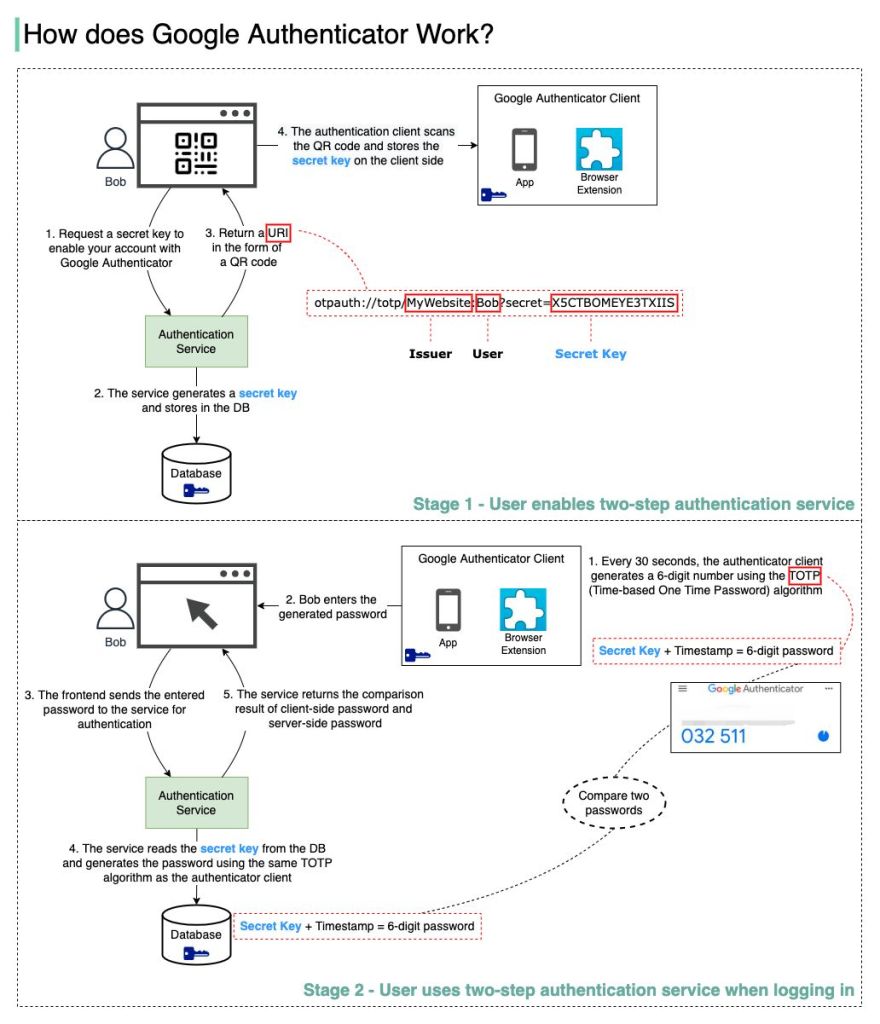
There are two stages involved:
- Stage 1 – The user enables Google two-step verification
- Stage 2 – The user uses the authenticator for logging in, etc.
Let’s look at these stages.
𝐒𝐭𝐚𝐠𝐞 1
Steps 1 and 2: Bob opens the web page to enable two-step verification. The frontend requests a secret key. The authentication service generates the secret key for Bob and stores it in the database.
Step 3: The authentication service returns a URI to the frontend. The URI is composed of key issuer, username and secret key. The URI is displayed in the form of a QR code on the web page.
Step 4: Bob then uses Google Authenticator to scan the generated QR code. The secret key is stored in the authenticator.
𝐒𝐭𝐚𝐠𝐞 2
Steps 1 and 2: Bob wants to log into a website with Google two-step verification. For this he needs the password. Every 30 seconds, Google Authenticator generates a 6-digit password using TOTP (Time-based One Time Password) algorithm. Bob uses the password to enter the website.
Steps 3 and 4: The frontend sends the password Bob enters to the backend for authentication. The authentication service reads the secret key from the database and generates a 6-digit password using the same TOTP algorithm as the client.
Step 5: The authentication service compares the two passwords generated by the client and the server, and returns the comparison result to the frontend. Bob can proceed with the login process only if the two passwords match.
Here’s an illustration of the above 2 stages
Is this authentication mechanism 𝐬𝐚𝐟𝐞?
- Can the secret key be obtained by others?
We need to make sure the secret key is transmitted using HTTPS. The authenticator client and the database store the secret key, and we need to make sure the secret keys are encrypted. - Can the 6-digit password be guessed by hackers?
No. The password has 6 digits, so the generated password has 1 million potential combinations. Plus, the password changes every 30 seconds. If hackers want to guess the password in 30 seconds, they need to enter 30,000 combinations per second.
Microsoft Vs. Google Authentication
Although there are other authentication apps, Google and Microsoft are the most widely used authenticators. However, the two apps differ slightly in terms of convenience and ease of use. For example, Microsoft provides a 30-second counter before the software token automatically resets instead of Google’s blue round fading countdown timer.
Furthermore, Microsoft has one-tap push notifications for all Microsoft Accounts, something that Google doesn’t provide. Microsoft also allows users to hide or copy the secret code. On the other hand, Google allows users to change email for all existing accounts.
Overall both authentication apps provide high-level security for all your devices to ensure your online services or data are protected.